There is a great imbalance in the vast internet marketplace that has yet to be addressed and is quite ripe for the picking. In fact, this imbalance is probably at the root of the astronomical stock market valuations of existing and new companies like Google, facebook, Twitter and their ilk.
There is a great imbalance in the vast internet marketplace that has yet to be addressed and is quite ripe for the picking. In fact, this imbalance is probably at the root of the astronomical stock market valuations of existing and new companies like Google, facebook, Twitter and their ilk.
It turns out that your data is valuable. Very valuable. And it also turns out that you are basically giving it away. You are giving it away – not quite for free but pretty close. What you are getting in return is personalization. You get advertisements targeted at you providing you with products you don’t need but are likely to find quite iresistable. You get recommendations for other sites that ensure that you need never venture outside the bounds of your existing likes and dislikes. You get matched up with companies that provide services that you might or might not need but definitely will think are valuable.
Ultimately, you are giving up your data so businesses can more efficiently extract more money from you.
If you are going to get exploited in this manner, it’s time to make that exploitation a two way street. Newspapers, for instance, are rapidly arriving at the conclusion that there is actual monetary value in the information that they provide. They are seeing that the provision of vetted, verified, thougful and well-written information is intrinsicly worth more than nothing. They have decided that simply giving this valuable commodity away for free is giving up the keys to the kingdom. The Wall Street Journal, the New York Times, The Economist and others are seeing that people are willing to pay and do actually subscribe.
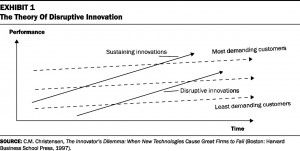
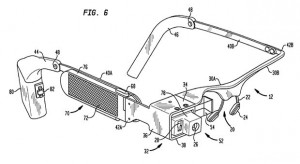
There is a lesson in this for you – as a person. There is value in your data. Your mobile movements, your surf trail, your shopping preferences It should not be the case that you implicitly surrender this information for better personalization or even a $5 Starbucks gift card. This constant flow of data from you, your actions, movements and keystrokes ought to result in a constant flow of money to you. When you think about it, why isn’t the ultimate personal data collection engine, Google Glass, given away for free? Because people don’t realize that personal data collection is its primary function. Clearly, the time has come for the realization of a personal paywall.
The idea is simple, if an entity wants your information they pay you for it. Directly. They don’t go to Google or facebook and buy it – they open up an account with you and pay you directly. At a rate that you set. Then that business can decide if you are worth what you think you are or not. You can adjust your fee up or down anytime and you can be dropped or picked up by followers. You could provide discount tokens or free passes for friends. You could charge per click, hour, day, month or year. You might charge more for your mobile movements and less for your internet browsing trail. The data you share comes with an audit trail that ensures that if the information is passed on to others without your consent you will be able to take action – maybe even delete it – wherever it is. Maybe your data lives for only a few days or months or years – like a contract or a note – and then disappears.
Of course, you will have to do the due diligence to ensure you are selling your information to a legitimate organization and not a Nigerian prince. This, in turn, may result in the creation of a new class of service providers who vet these information buyers.
This data reselling capability would also provide additional income to individuals. It would not a living wage to compensate for having lost a job but it would be some compensation for participating in facebook or LinkedIn or a sort of kickback for buying something at Amazon and then allowing them to target you as a consumer more effectively. It would effectively reward you for contributing the information that drives the profits of these organizations and recognize the value that you add to the system.
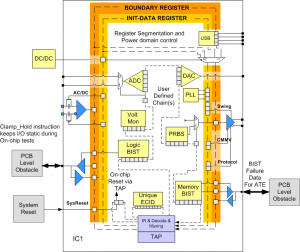
The implementation is challenging and would require encapsulating data in packets over which you exert some control. An architectural model similar to bitcoin with a central table indicating where every bit of your data is at any time would be valuable and necessary. Use of the personal paywall would likely require that you include an application on your phone or use a customized browser that releases your information only to your paid-up clients. In addition, some sort of easy, frictionless mechanism through which companies or organizations could automatically decide to buy your information and perhaps negotiate (again automatically) with your paywall for a rate that suits both of you would make use of the personal paywall invisible and easy. Again this technology would have to screen out fraudulent entities and not even bother negotiating with them.
There is much more to this approach to consider and many more challenges to overcome. I think, though, that this is an idea that could change the internet landscape and make it more equitable and ensure the true value of the internet is realized and shared by all its participants and users.